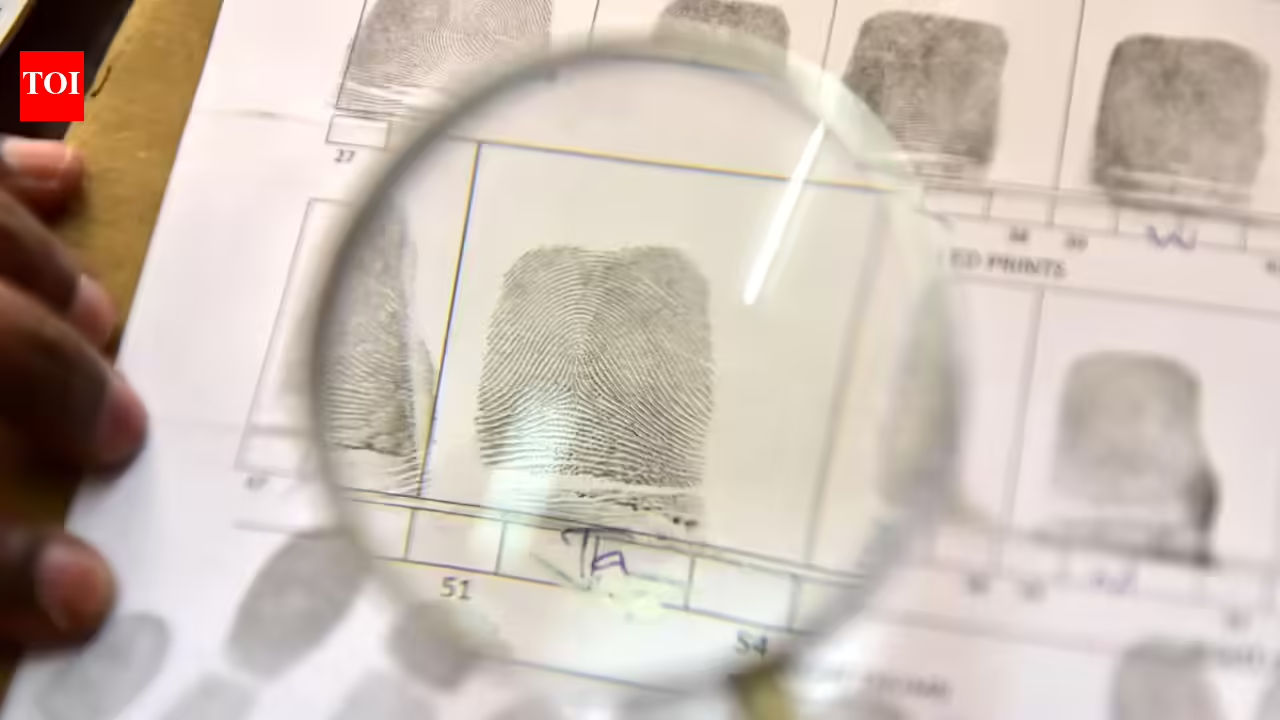
TNNJaipur: Four days after arresting a man for allegedly using forged biometric data to generate Aadhaar cards in Hanumangarh, Rajasthan Police have widened their probe, placing multiple Aadhaar numbers under scrutiny and launching a statewide audit of enrollment records.Police said the accused, Kuldeep Sharma, was part of a racket that operated several unauthorized enrollment centers using stolen operator IDs and created Aadhaar identities with dummy rubber fingerprints. Investigators found the gang used both red and white rubber molds to bypass biometric verification and gain unauthorized access to the system.Officials in the Rajasthan ATS said they are coordinating with the state’s Dept of Information Technology (DoIT) to retrieve data of cards generated through the compromised operator IDs on Tuesday. “We are mapping every ID issued through these terminals to identify patterns and possible misuse,” a senior officer said.Preliminary findings suggest the racket may have been active for months, with enrollments carried out at multiple locations to avoid detection. Police suspect several individuals with criminal backgrounds may have obtained Aadhaar cards through the network, enabling them to evade law enforcement or assume new identities.The probe has also been expanded to track financial links tied to the forged IDs. Officers suspect the fake Aadhaar cards were used to open bank accounts that may have served as conduits for parking illicit funds or routing proceeds of cybercrime.Sources said forensic teams are analyzing seized devices, including biometric scanners and laptops, to determine how system safeguards were bypassed. Investigators are also examining whether insiders or authorized operators knowingly shared credentials or if the IDs were compromised through other means.
Raj ATS widens Aadhaar probe, dummy fingerprints used. Jaipur News
Investigators found the gang used both red and white rubber molds to bypass biometric verification and gain unauthorized access to the system. TNNJaipur: Four days … Read more
Previous Post
Next Post
Leave a Reply
Latest News

Stay Connected
Categories
Tags
Asha Bhosle Bhubaneswar latest news Bhubaneswar news Bhubaneswar news live Bhubaneswar news today bjp Breaking news Donald Trump Goa latest news Goa news Goa news live Goa news today Google news Guwahati latest news Guwahati news Guwahati news live Guwahati news today India India News India news today ipl IPL 2026 Kolkata Knight Riders Lucknow Mumbai Indians New Delhi Patna latest news Patna news Patna news live Patna news today Rajasthan Royals Ranchi latest news Ranchi news Ranchi news live Ranchi news today Ranveer Singh Royal Challengers Bengaluru Strait of Hormuz Today news Today news Bhubaneswar Today news Goa Today news Guwahati Today news Patna Today news Ranchi Uttar Pradesh
About the Author

AF themes
Easy WordPress Websites Builder: Versatile Demos for Blogs, News, eCommerce and More – One-Click Import, No Coding! 1000+ Ready-made Templates for Stunning Newspaper, Magazine, Blog, and Publishing Websites.
Search the Archives
Access over the years of investigative journalism and breaking reports
You May Have Missed